[ad_1]
Disclosure: The views and opinions expressed here belong solely to the author and do not represent the views and opinions of crypto.news’ editorial.
A recent landmark report from Elliptic revealed an eye-popping $7 billion in illicit crypto assets has been laundered through cross-chain services. What does that actually mean? Essentially, criminal organizations are utilizing decentralized exchanges, cross-chain bridges, and coin-swapping services to cover up the tracks and origins of funds from illegal sources.
Seven billion of US dollars is a worrisome figure and exposes a clear blind spot in stamping out money laundering through loopholes and processes in decentralized financial frameworks. And if we take Elliptic’s report at face value, it also signals that illicit actors have moved on from crypto mixers to use bridges as a bona fide tool for money laundering and other financial crimes.
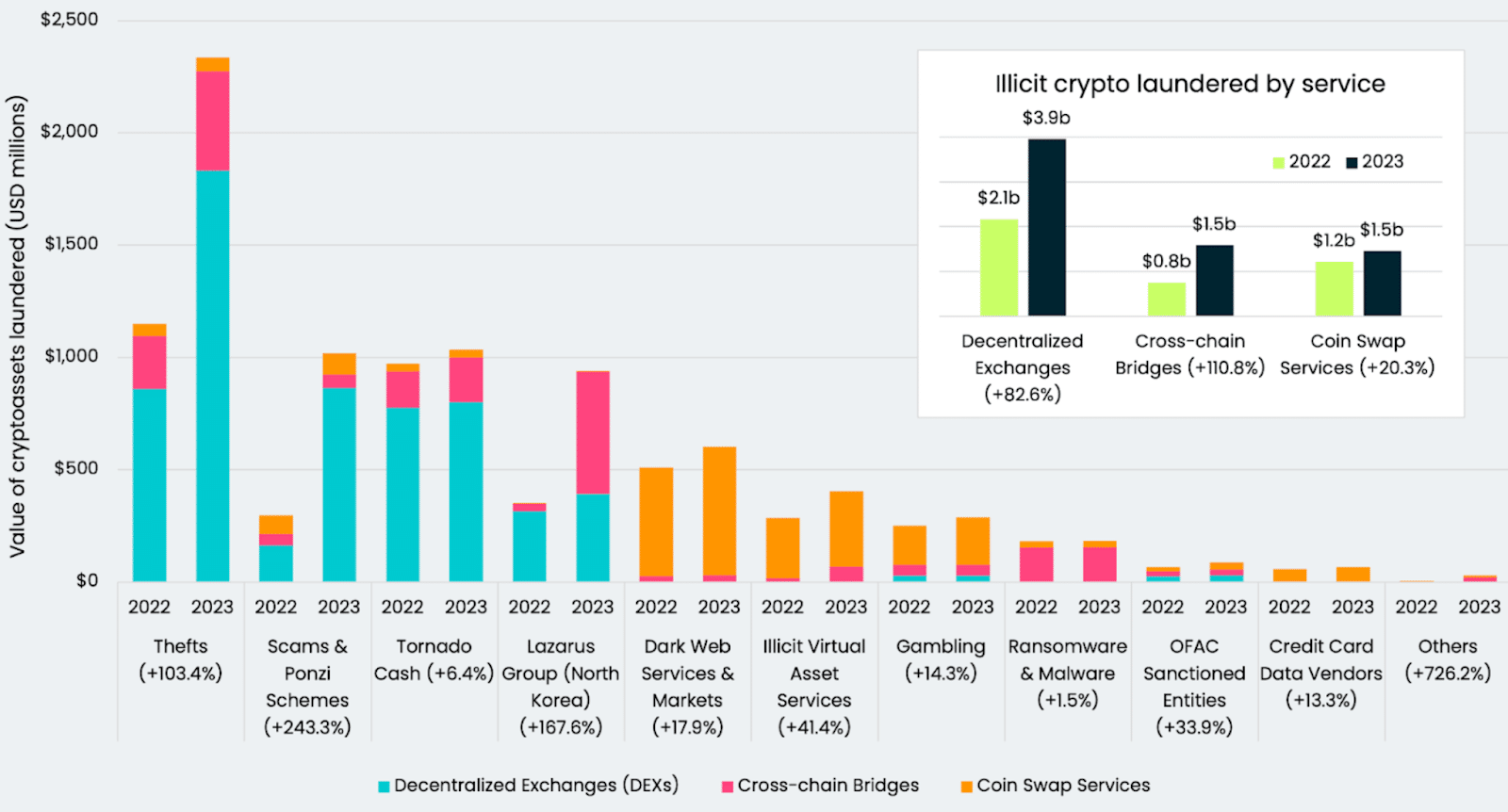
The state of cross-chain crime by predicate offense and service used | Source: Elliptic
We can either accept or ignore that bridges are being used for these purposes and chalk it up to being a fact of life in defi. But that approach doesn’t solve any problems in squashing crypto money laundering—it only sweeps it under the rug.
It’s not as though these tools are built with criminal activity in mind. If anything, they embody crypto’s fundamental tenets of preserving privacy and streamlining transactions by removing the red tape. However, their misuse in fostering illicit transactions and illegal fund transfers shows how a benevolent service can become weaponized.
For instance, based on how cross-chain bridges inherently function, it’s easy for criminals to move funds from a well-known address on one chain to a brand new address on the second chain, severing the knowledge chain as they please. The transfer process either wraps the funds or removes them from pooled liquidity, rendering them effectively untraceable. The bridge effectively acts as a getaway car.
We’ve seen this narrative of misuse play out several times in crypto even beyond mixers, with crypto exchanges once being a hotbed for money laundering and financial crime. Much like exchanges 5-10 years ago, there’s no sort of ‘passport control’ for these bridges. While you could say that this is a phase that bridges will phase out of much like centralized exchanges eventually did, their use as a money laundering channel to such an extreme cannot be ignored.
So how can this rampant abuse of crypto’s infrastructure get reined in?
Right now, the most significant blind spot for crypto crimes on cross-chain bridges stems from a distinct lack of anti-money laundering (AML) protocols within their frameworks. While some chains try to retain the knowledge chain that connects the two networks together by not allowing users to specify a different destination address, that only works when both blockchains are EVM-based. Even then, their functionality and scope are limited to the detection intelligence on the destination blockchain—allowing illicit activities to still slip through the cracks.
The typical response here would be to say that bridges must go in the opposite direction of how they operate now. Put in extensive KYC and AML measures to prevent money laundering or other financial crimes and the problem’s solved—even if it means having to undergo KYC controls to bridge $20 in assets and create an expensive, cumbersome, and unfriendly UX.
But there is another way that’s rooted in buffing up AML practices. While KYC and AML often do go hand-in-hand, they’re not the same thing and don’t function in the same way. Yes, there’s an overlap, but conflating the two as being interchangeable is inaccurate.
Cross-chain bridges can still function anonymously or pseudonymously while still implementing AML guardrails that don’t explicitly involve heavy KYC barriers. The point isn’t to expose everyone to bridging any asset, but just to ensure that money being transferred between chains isn’t being done by an illicit force that just stole it and wants authorities to lose track of it. But that will take a few changes to fully realize.
A seemingly simple solution to stop money laundering in its tracks would be for regulators to pass mandates dictating AML parameters that bridges must meet to operate. But we all know that attaining regulatory clarity for blockchain products is anything but simple—and allowing exploitation to happen in the meantime only worsens regulatory attitudes.
From a technical perspective, that could involve instituting some level of permission into bridging infrastructure and implementing some form of anomaly detection that isn’t so invasive. Preserving trustlessness and privacy as much as possible while still preventing financial crimes is certainly feasible.
Technical solutions, then, are entirely up to the bridge’s developers to implement. But since most bridges are implemented as decentralized protocols, and without a mandate to force them into doing so, most projects don’t see the need to implement any AML measures. While that attitude is incredibly short-sighted, it does reflect the reality of cross-chain services not wanting to step on the toes of decentralization purists or alienate their audience by introducing more steps into the transaction process.
That approach has to change quickly. Developers should take the steps necessary to implement technical solutions and controls to instill AML capabilities into their frameworks as all activities take place on-chain. While that might ring the alarms of developers who don’t want to add another intermediary or red tape into defi, that’s not necessarily the case.
Since blockchain activity can be embedded beneath several composability layers, protocols must implement a solution that operates at the heart of where it takes place. That means implementing real-time on-chain AML protocols. That comes in the form of sanctions, fraud detection, and prevention checkpoints or encouraging on-chain transparency for any transactions or activity. Being proactive in creating deterrence measures for illicit activities will only help a protocol remain credible in the long run while keeping its users safe.
If blockchain and crypto as a whole are to be adopted on a wide scale, ensuring that its frameworks are not being used to fund terror, oppressive regimes, or illegal businesses at the expense of other users becomes paramount. Yes, you could argue that money laundering still happens in the traditional financial industry and this would only help put a band-aid on a wider issue. But putting pressure on bridges and other cross-chain services to heighten their AML and fraud prevention practices ultimately benefits everyone and helps crypto live up to its full potential as an intermediary-free financial ecosystem.
[ad_2]